In this section, we'll take a look at determining where best to start a packet capture for the troubleshooting scenario. Now, in this troubleshooting scenario, we have a user that is reporting that they're unable to access the FTP server. They start with their client, and it just says that the connection does not work.
Now, what we need to do is determine where we need to begin packet captures in order to figure out what's going on:
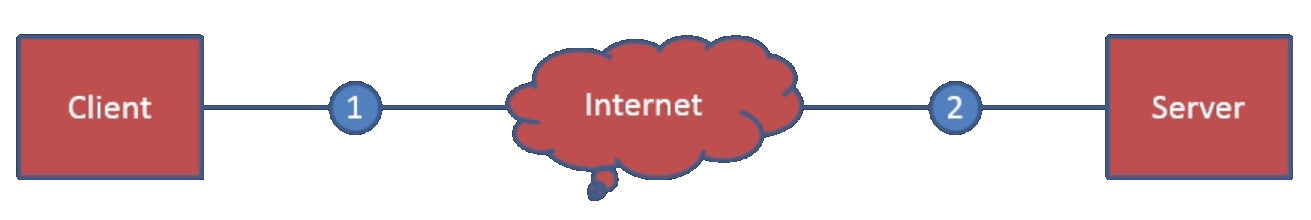
There might be an issue on the client side; there might be an issue on the server side; or there might be an issue somewhere in between on the internet, possibly. Maybe it's a routing issue, or something like that that's out of our control. So besides taking a look at log files on the client or the server, we'll take a look at the packet captures themselves. Additionally, there might be a problem somewhere between the client and the internet, or between the internet and the server. These intermediary devices could be firewalls or routers, or something else that might be blocking or causing issues with the connection. With this scenario, since the client is reporting a problem but is not being very specific, we'll start out with a packet capture on the client side. Then, if we determine that we might need some additional packet captures, we will capture on the server side.
Normally, when you are capturing, you'll start from the most easily accessible location or closest to the issue at hand, and then work your way along the data path. If a client is reporting a problem, then you will most likely be trying to do a packet capture on the client side, and then, if you do not see any sort of obvious issue as to what's going on, then you work your way up. You go to the next intermediary device, such as numbers 1 and 2 on this diagram, and then you go from there; and you might have to get involved with the ISP. Then, you continue your way along that data path from source to destination, performing packet captures to help determine what the issue is.
