We'll start a new capture and then traceroute. In Windows, it's tracert. We will traceroute to a different device out there on the internet.
We will traceroute out to our trusty Google DNS server; why not? We will then press Enter, and we see the path start to show up here:
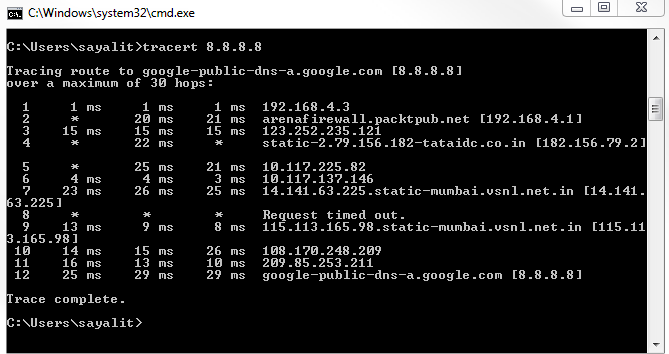
You can see that it has received a number of responses as it went through each different router. Every once in a while you'll notice that it gets some timed-out responses. Depending on the router or firewalls that it goes through, they may not send back information to us. This is why sometimes you'll get gaps in your path, but you can see that it picks up again as it finds another router that responds to us at least. Hence, we're still going through the internet, bouncing through routers, and eventually getting to our destination. If you've noticed, each one of these hops was done three times. So, it gives us an average of the response time for that specific router over an average of three attempts—it goes from router to router.
If we take a look at Wireshark, we should see three requests for each router. What it does in my system is, when it creates a traceroute, it starts out by sending a packet to my destination with a TTL of 1, not 128 or 60, or anything like that:
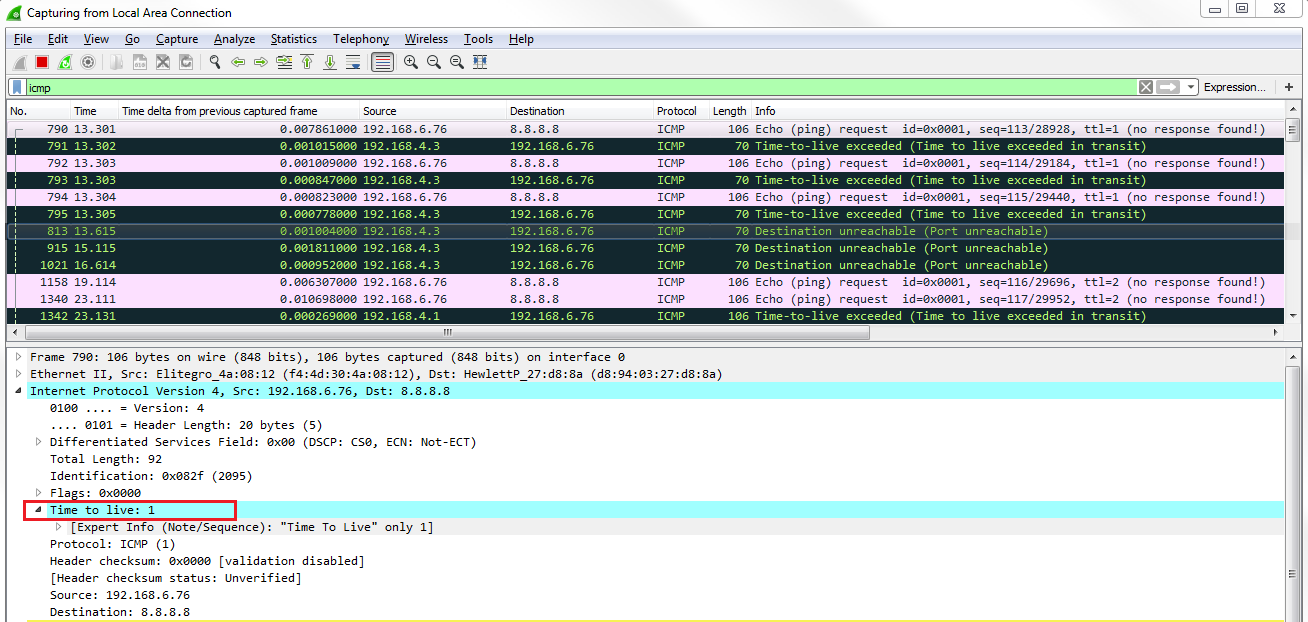
So it'll go to our router that will get it and say, "I can't do anything with this; I need to discard it". The TTLs will go to 0. Then our router will send an ICMP back to me, letting us know that my TTL has been exceeded. What we can see is that's exactly what happens. We sent out a ping request, an echo request with a TTL of 1. Our router responded to say "oh, sorry; I couldn't do it". Then, I do it again for that second attempt. We get a response that says "no, I can't do it". This is done a third time, as well. Then, it goes and creates an echo request with a TTL of 2:
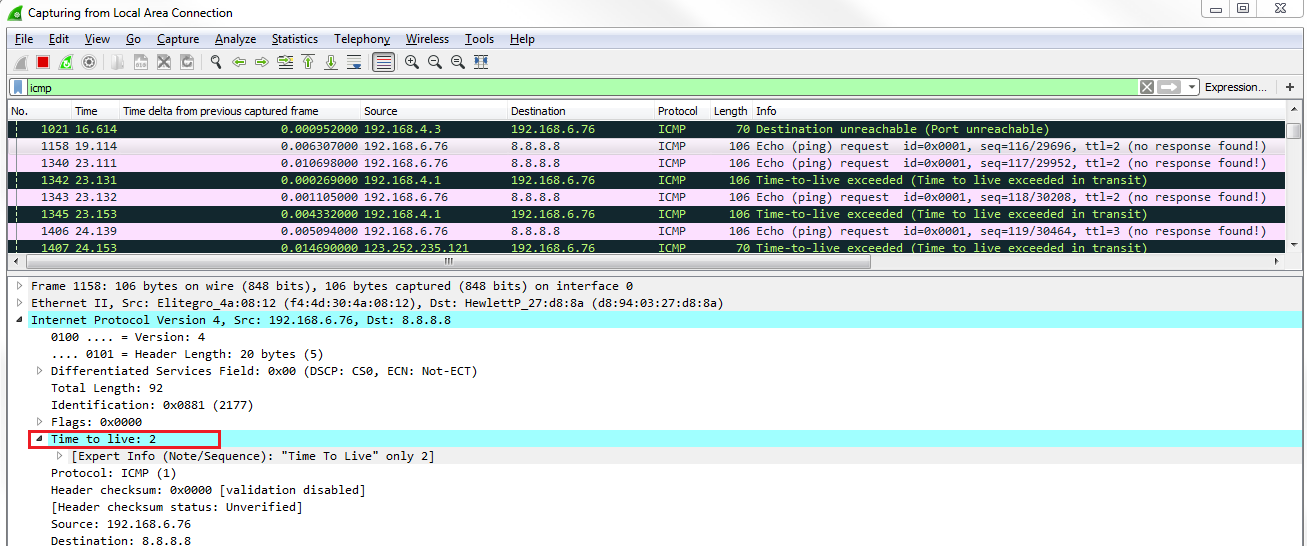
It gets through our router because my router sees that it's a 2; it decrements it to 1 and forwards it; that's completely valid. Then it goes to the next router up the chain, on Verizon, we saw. That router sees it; it sees that it's a TTL of 1; it has to discard it and send back a response saying "no, sorry; I couldn't do it; your TTL has exceeded". I do it again and it responds. Now, we create a TTL of 3:
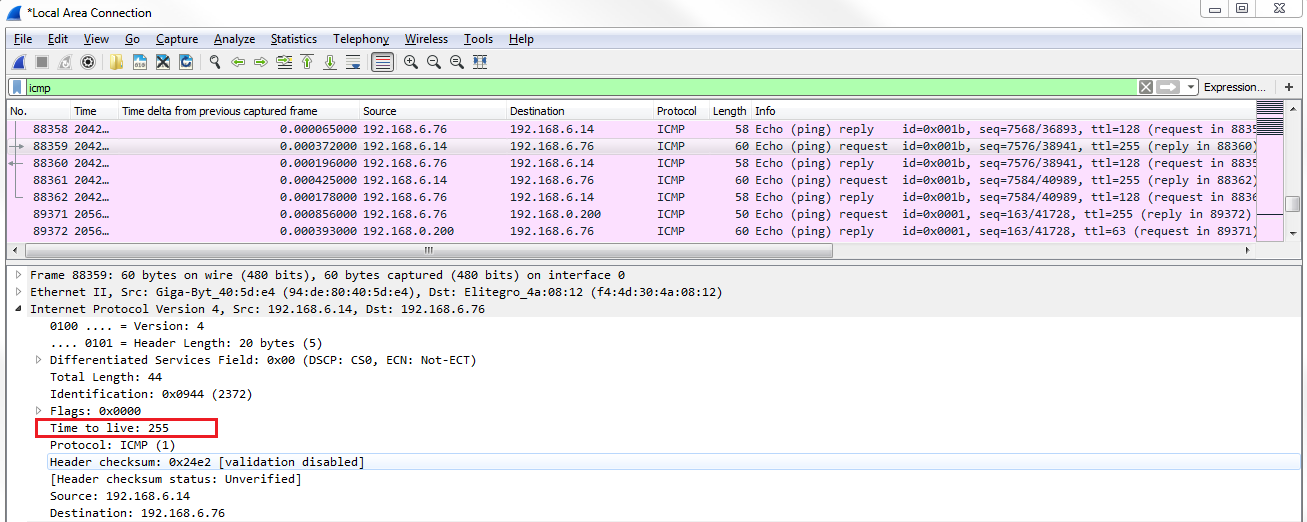
It keeps doing that for TTL 4 and so on. That's how traceroute is able to map out the routers from point A to point B—because it uses the ICMP TTL exceeded errors in order to figure out that device. This is because it knows that the ICMP packet is generated by the router as an error code back to us. Luckily, we can use that IP information to map out the hops that I go through in order to get to that destination. Very clever.
