Now, in the second example, we'll take a look at NS. Let's say, you have some sort of problem in your network where certain DNS responses are coming back if they can't find any sort of records in your DNS server for a resource, whether it's a web page or a local server; whatever it is, it's not finding the DNS entries. We can apply a coloring rule that will vibrantly show us whenever there's a DNS response that it cannot find a record.
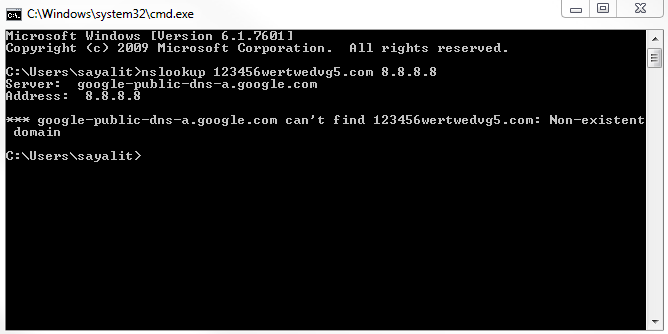
Let's go ahead and create a new capture, and I'm going to look up some random web page that doesn't exist, and we'll use DNS off of Google. We will get a message that it doesn't exist:
So we're going to stop our capture, and we'll see nothing really pops out. There would be some red stuff there from some TCP resets and some black ones, but nothing else. It's all TCP traffic and DNS. Let's go ahead and create a coloring rule:
- Make a new coloring rule by clicking on View | Coloring Rules...; we'll call it DNS No Records.
- In the filter information, we'll enter dns.flags.rcode, which is for the response code. If the response code equals 3, it means there's no record:
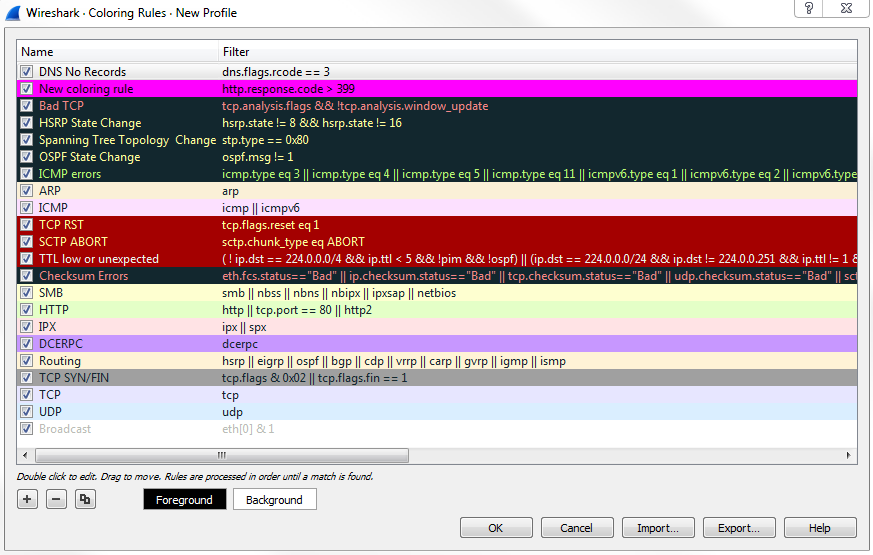
- We will select the Foreground as black and Background as yellow.
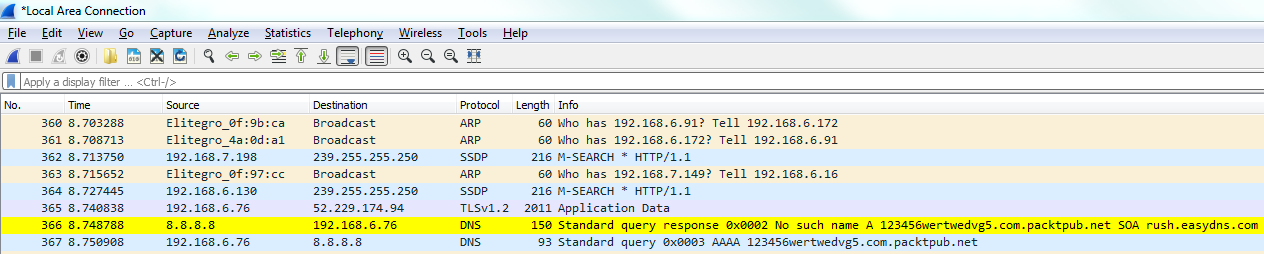
Now, let's go ahead and scroll through our packet capture and see if we can find this response code error. We can see our Standard querie response 0×0002 No such name A record, and then the random gibberish that we entered in. And then of course it's also responding for IPv6. The AAAA, the quad A record, is for IPv6, as well:
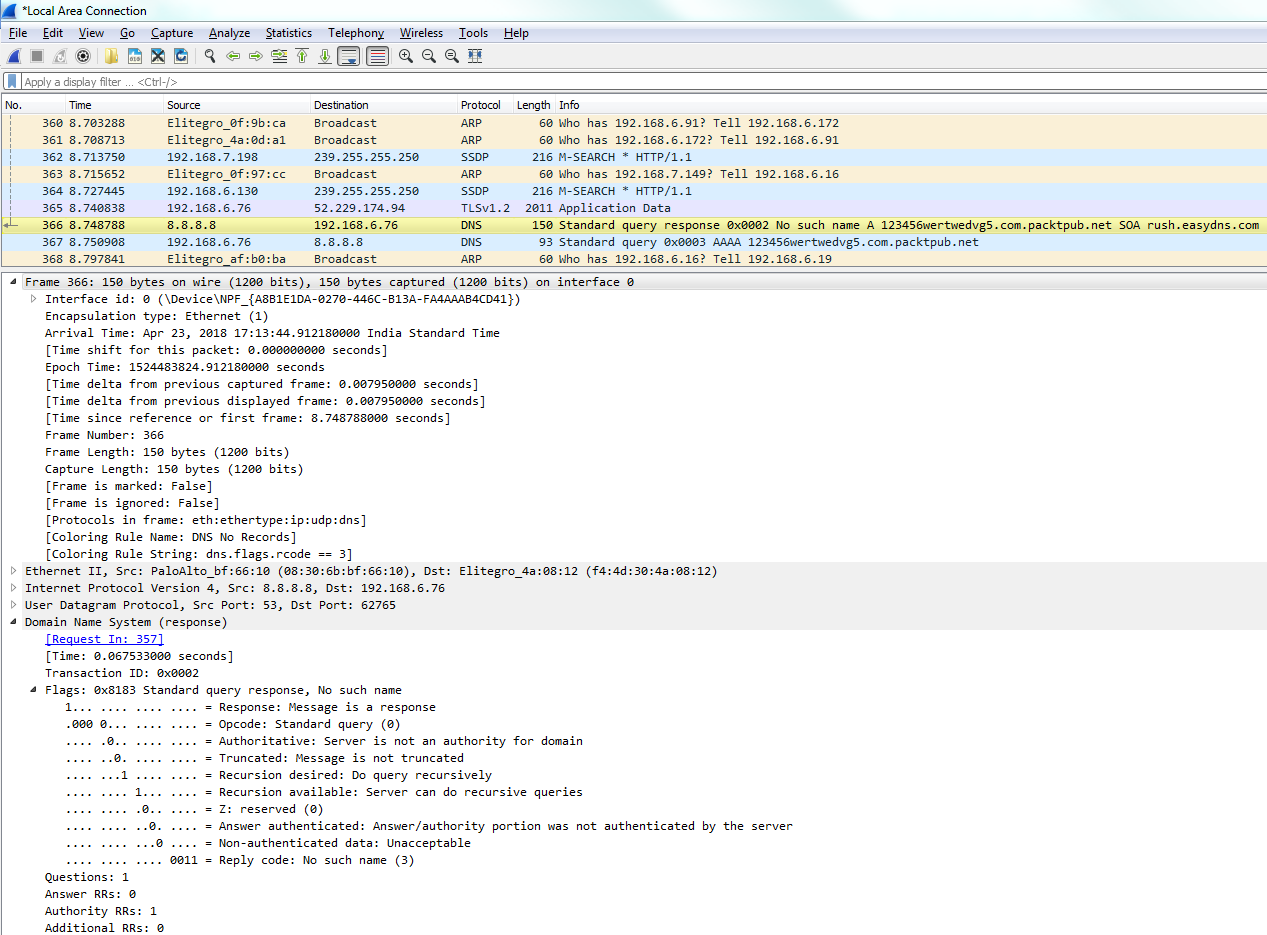
If you take a look in our frame information at the bottom, there's our coloring rule: DNS No Records. There's a string that it's using, and if we dig into the DNS information, you look at the flags and it will say Reply code: No such name (3). That's the value of 3 that we just filtered on:
You can see how applying coloring rules can be very helpful to someone who's doing network analysis and protocol analysis because it makes it very easy to pick out from a large packet capture wherever there's a problem.
