In this section, we'll take a look at capturing some traffic for our troubleshooting scenario, and checking for some obvious issues before we look into the packet capture a bit more in-depth.
In the following screenshot, we have captured the traffic from the client connecting to the server:
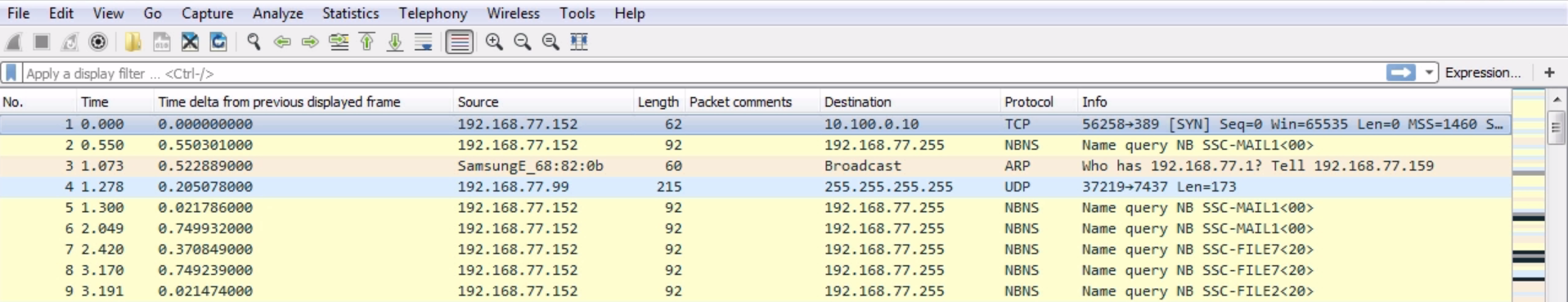
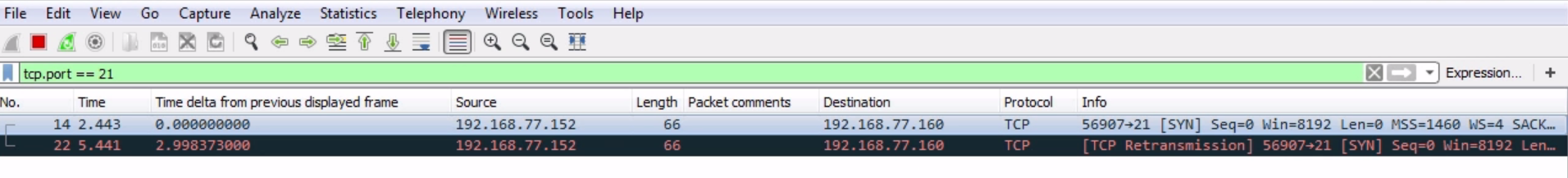
We will now put a filter in here for port 21 because we know that the client is connecting over standard unencrypted FTP. For that we use tcp.port == 21:
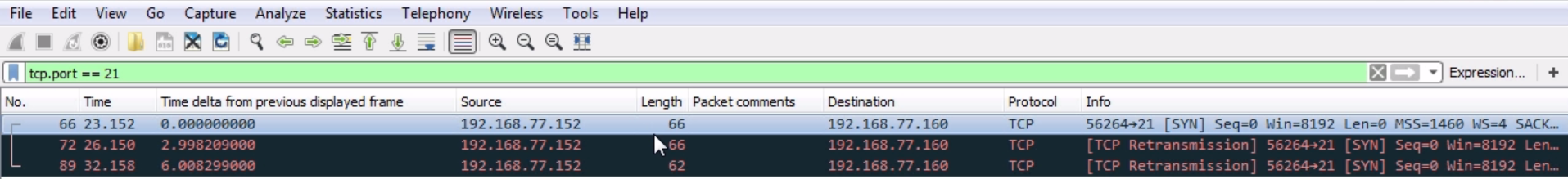
So, we got rid of everything else. We can see that there are three packets, and it looks like we have a SYN and two retransmissions. So the client, which is .152, is trying to connect to the server running on .160, and it's not even beginning the TCP handshake. So the server is not doing something correctly in order to negotiate port 21. It's not that the server is rejecting the user credentials or there's some sort of other obvious issue. It's definitely not listening on 21 or something like that. Let's start a capture on the server side, and when the client connects, we'll see what it does as well:
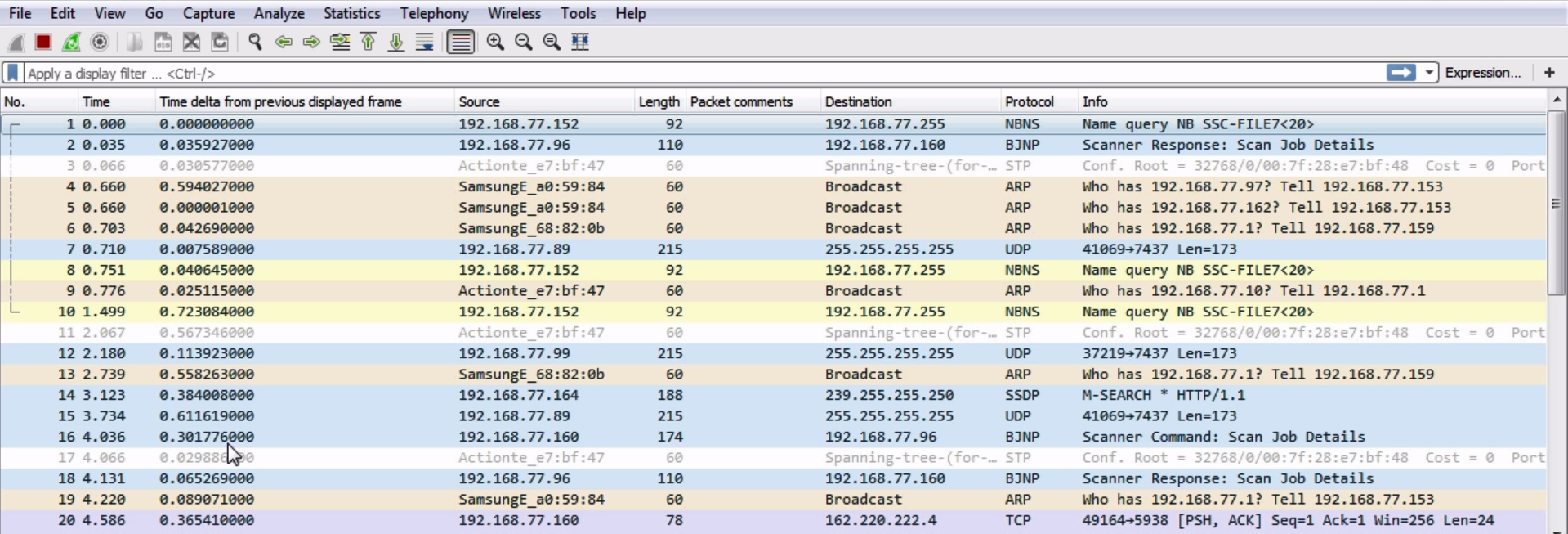
We have the server running, so let's go ahead and try our login attempt. You can see the packets updating and the client's trying to connect, and you can see that it has failed. So we'll stop that and also our capture, and then we'll do what we did earlier.
Let's enter tcp.port == 21 and see what happens:
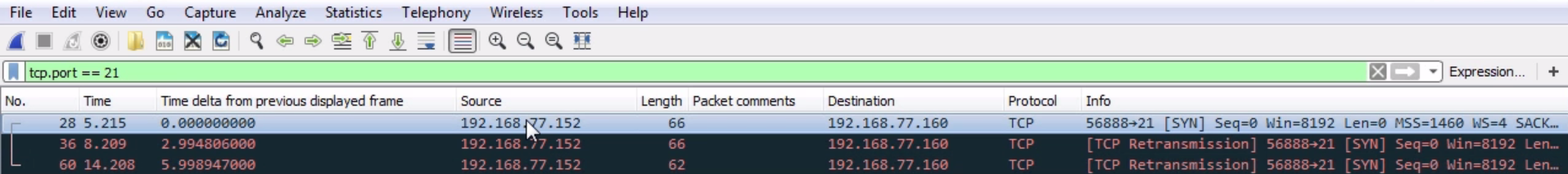
So on the server side, it looks identical. What we're seeing is the source coming into the server as the 152 client, hitting the server's destination IP 160. It's reaching the server at least, so we know that the IP is working correctly. We'll get a SYN, then a retransmission from the client, and then we'll get another retransmission. Obviously, something on the server's not running correctly. Since that's pretty obvious, let's take a look and see whether our FTP server's even running correctly. Let's take a look at our services in here:
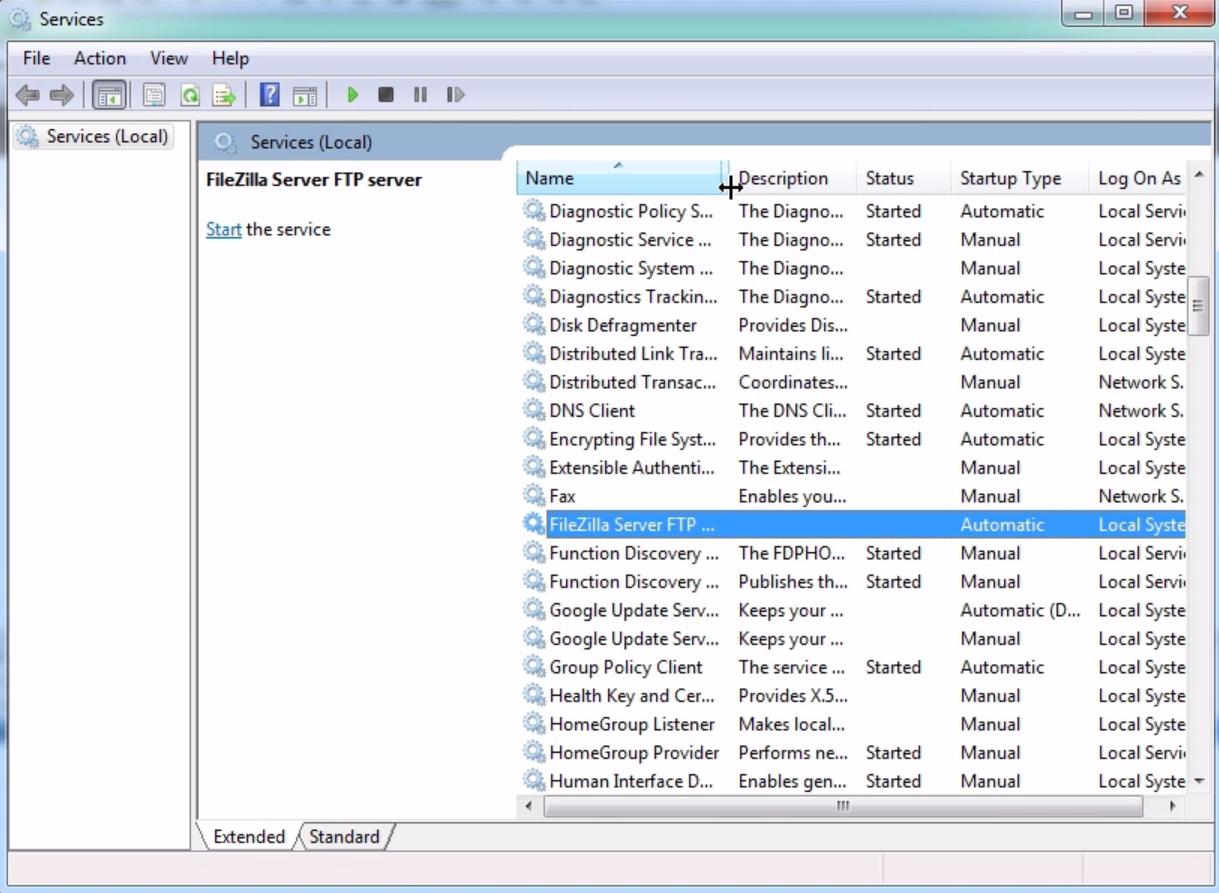
You can see that we have the FileZilla FTP server that's supposed to be running, but it's not started. Let's go ahead and start this service:
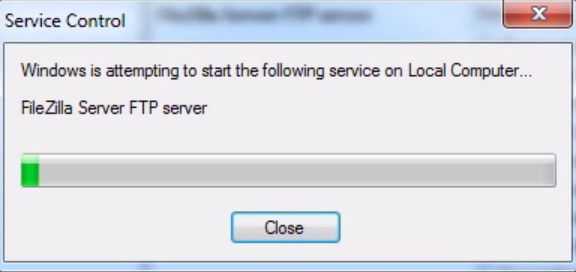
Now our server's running and we know that everything looks good; we'll refresh just to make sure; then, let's go ahead and start another capture on the server.
From the client, we will begin a connection, and we can see this:
So we have a SYN, a retransmission again, and another retransmission. The server is running and the service is operational. What we can also do is check our ports that are listening on the server with netstat -an:
netstat -an
Now, let's take a look at port 21:
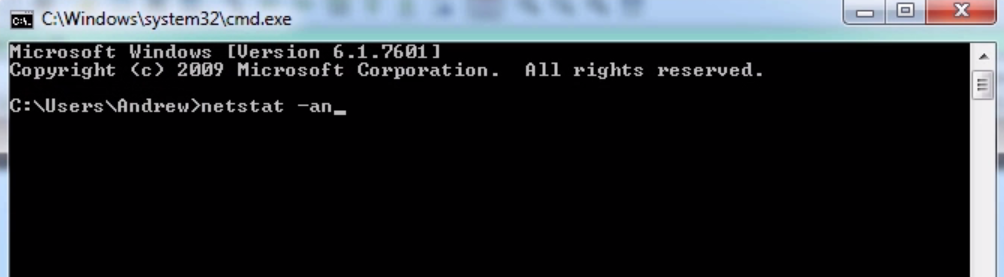
We can see here that we do have port 21 listening on the server, so the service is running correctly. It looks like we'll need to investigate the server a little bit further, and take a look at the packet capture once we eventually get this SYN connectivity issue resolved in the next section.
Now we'll actually perform these packet captures. We'll dive into the diagnostics of our connection issue with FTP here a little bit further.
