Zenmap is the graphical interface of Nmap. The advantages of Zenmap compared to Nmap are as follows:
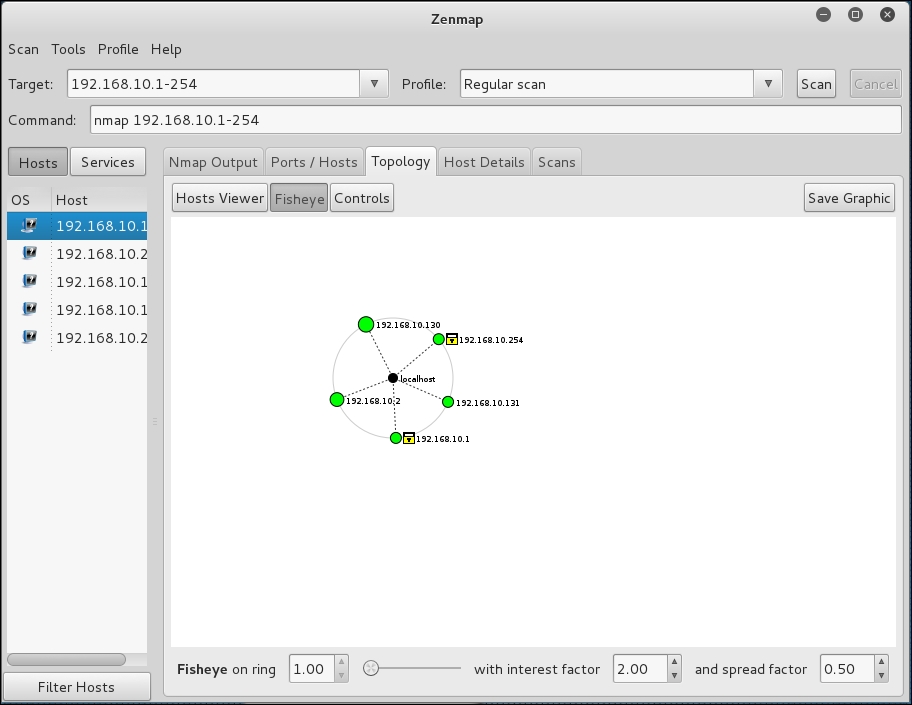
- Zenmap is interactive; it arranges the scan results in a convenient way. It can even draw a topological map of the discovered network.
- Zenmap can do a comparison between two scans.
- Zenmap keeps a track of the scan results.
- To run the same scan configuration more than once, the penetration tester can use a Zenmap profile.
- Zenmap will always display the command that is run, so the penetration tester can verify that command.
To start Zenmap, navigate to Kali Linux | Information Gathering | Network Scanners | Zenmap, or use the console to execute the following command:
#zenmap
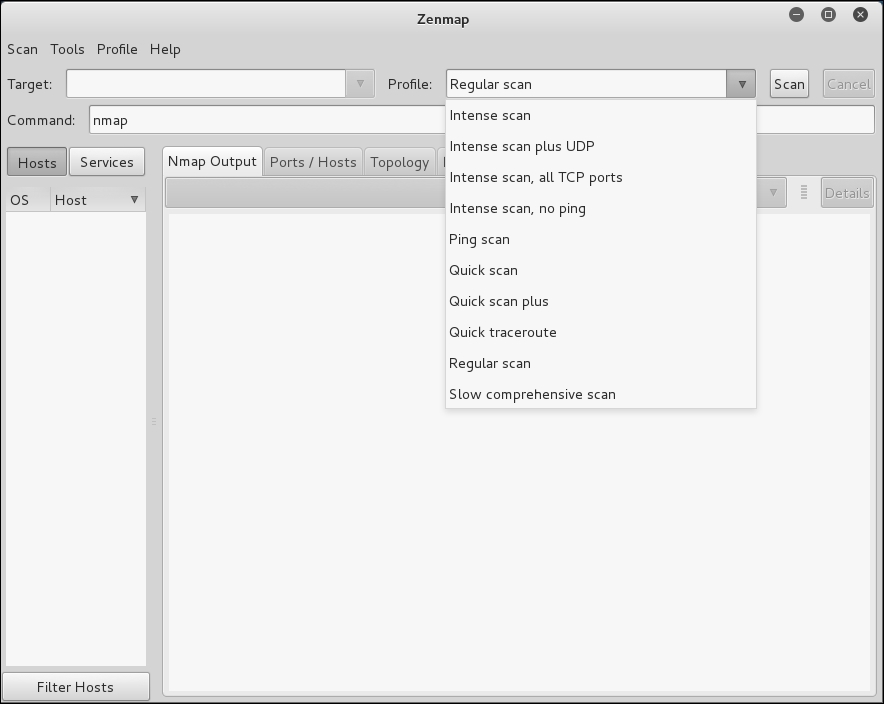
This will display the main Zenmap window. Zenmap comes with 10 profiles that can be chosen. To find which command options are used on each profile, just click on Profile and the command options will be displayed in the Command: box, as shown in the following screenshot:
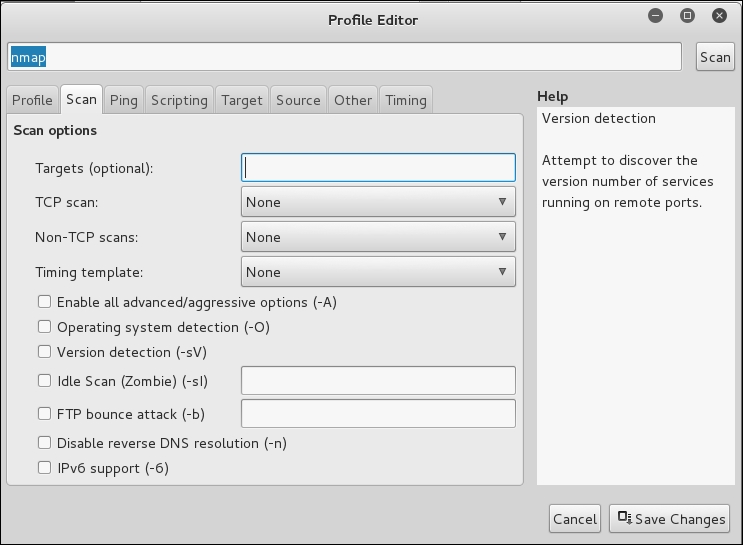
If the provided profiles are not suitable for our needs, we can create our own profile by creating a new profile or editing the existing ones. These tasks can be found under the Profile menu.
To create a new profile, select the menu New Profile or Command, or you can press the keys Ctrl + P. To edit an existing profile, select the Edit Selected Profile menu or press Ctrl + E.
Select each tab (Profile, Scan, Ping, Scripting, Target, Source, Other, and Timing) and configure it according to your needs. If you have finished configuring the profile, save the profile by clicking on the Save Changes button, as shown in the following screenshot:
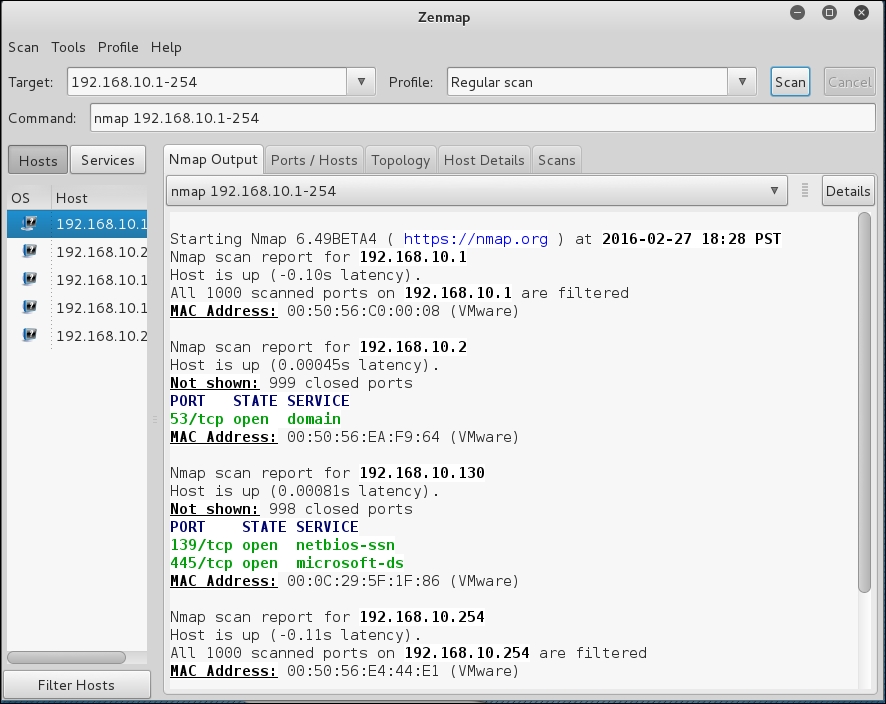
Let's scan the 192.168.10.1-254 host using the Regular scan profile, as shown in the following screenshot:
If you want to see the network topology, click on the Topology tab and you will be able to see the details, as shown in the following screenshot:
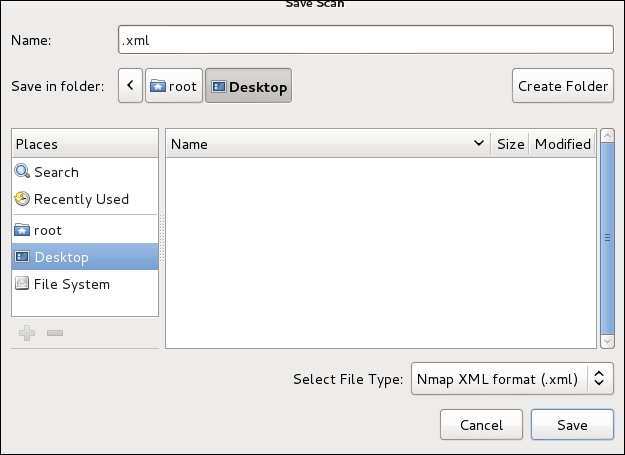
To save the Zenmap result, go to the Scan menu and choose Save Scan. Zenmap will then ask you where you want to save the result. The default format is XML, as shown in the following screenshot:
To find the differences between the scans, perform the first scan and then save the result. Then, make changes to the scan targets. Next, do the second scan and save the result. Later, compare the scan results by going to the Tools menu and selecting Compare Results.
For A Scan, you can select the XML file of the first scan result by clicking on the Open button, while for B Scan, you can select the XML file of the second scan result, as shown in the following screenshot:
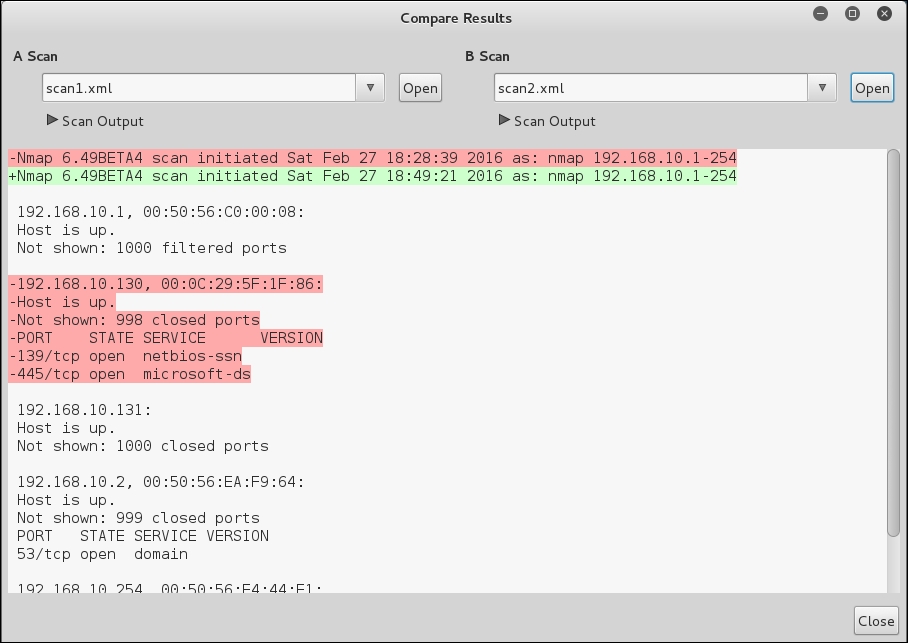
The - character denotes that this line is removed in the B Scan result, while the + character means that this line is added in the B Scan result.
What we notice is that there was an entire host that was visible on the first scan but not the second. This feature also allows the tester to view ports that have been open or closed over time. This is very handy if a target network has a new open port that is indicative of a specific piece of software. This is also handy if you are scanning a large network and want to see if devices have been added or removed.
