The art of virus writing has been around for several decades now. In fact, it goes all the way back to the Elk Cloner Apple virus that was successfully launched in the wild in 1981 through a floppy disk video game. Since the mid '80s and through the '90s, there have been various secret groups and hackers who have used their arcane knowledge to design, release, and publish viruses in virus and hacker e-zines (see http://vxheaven.org/lib/static/vdat/ezines1.htm).
The art of virus writing is usually of great inspiration to hackers and underground technical enthusiasts, not because of the destruction that they are capable of, but rather the challenge in designing them and the unconventional coding techniques that are required to succeed in programming a parasite that keeps its residency by hiding in other executables and processes. Also, the techniques and solutions that come with keeping a parasite stealthy, such as polymorphic and metamorphic code, present a unique challenge to programmers.
UNIX viruses have been around since the early '90s, but I think many would agree to say that the true father of the UNIX virus is Silvio Cesare (http://vxheaven.org/lib/vsc02.html), who published many papers in the late 90s on ELF virus infection methods. These methods are still being used today in different variations.
Silvio was the first to publish some awesome techniques, such as PLT/GOT redirection, text segment padding infections, data segment infections, relocatable code injection, /dev/kmem patching, and kernel function hijacking. Not only that, but he personally played a big role in my introduction to ELF binary hacking, and I will always remain grateful for his influence.
In this chapter, we will discuss why it is important to understand ELF virus technology and how to design them. The technology behind an ELF virus can be utilized for many things other than writing viruses, such as general binary patching and hot patching, which can be used in security, software engineering, and reversing. In order to reverse-engineer a virus, it would behoove you to understand how many of them work. It is worth noting that I recently reverse-engineered and wrote a profile for a unique and exceptional ELF virus called Retaliation. This work can be found at http://www.bitlackeys.org/#retaliation.
The world of ELF virus technology shall open up many doors to you as a hacker and engineer. To begin, let's discuss what an ELF virus is. Every executable program has a control flow, also called the path of execution. The first aim of an ELF virus is to hijack the control flow so that the path of execution is temporarily altered in order to execute the parasite code. The parasite code is usually responsible for setting up hooks to hijack functions and also for copying itself (the body of the parasite code) into another program that hasn't yet been infected by the virus. Once the parasite code is done running, it usually jumps to the original entry point or the regular path of execution. This way, the virus goes unnoticed, since the host program appears to be executing normally.
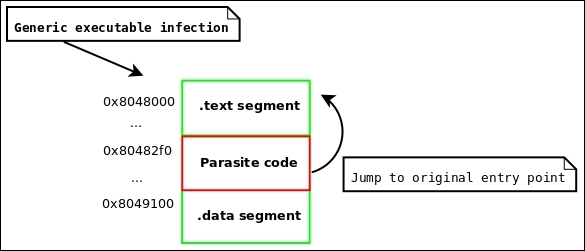
Figure 4.1: Generic infection to an executable
